GET Mobile ID
Make the Move to Secure Digital ID with GET Mobile ID
GET Mobile ID Digital Identity Solution
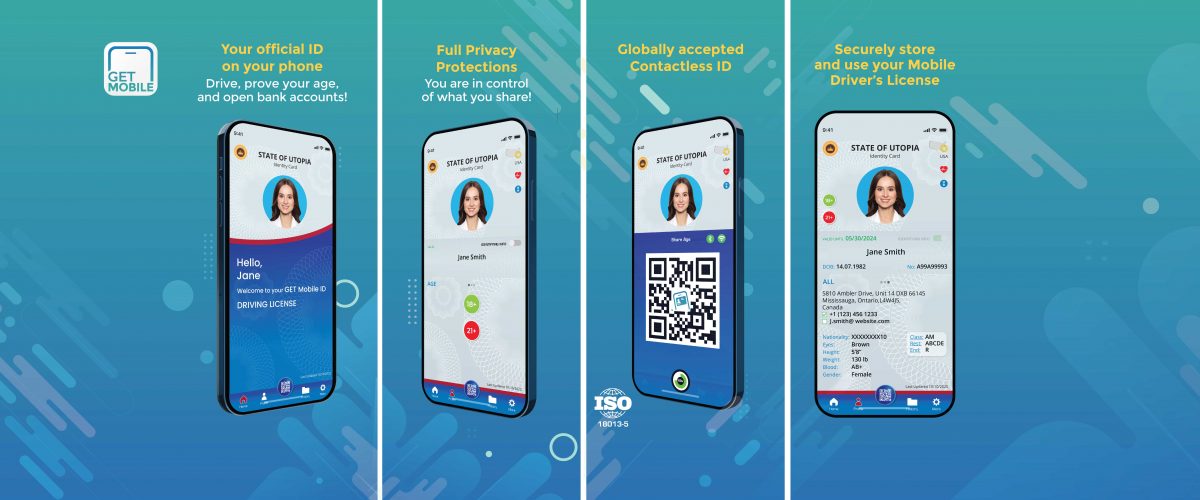
GET Mobile ID is the natural progression of your physical ID. As the world around you is going digital, so too is your ID card! Simple visual representation is now changing to a more secure credential, which will help you take control of your identity. You choose what data you want to share on your Mobile ID, without it ever leaving your hands. Whether it’s displayed as a QR code, simply shared with an NFC tap, or remotely beamed using Bluetooth, GET Mobile ID implements all transaction modes in the ISO 18013-5 standard to ensure users have as many options for sharing as possible.
Using state-of-the-art encryption techniques, GET Mobile ID implements security measures to ensure that your data remains just that; yours. You are in control of what data is shared. Gone are the days of having to show all your information when conducting age-restricted purchases; now you simply share your age and nothing else. Need to prove your residence? You can choose to share only your address.
GET Mobile ID is always up to date: as a holder, you’re always holding the most recent version of your license; as a verifier, you’re sure that what you are scanning is a legitimate, up to date document. Eliminate the chances of accepting fakes by using GET Mobile ID!
- Direct to consumer app enables citizen control of mDL
- Your official ID on your phone
- Use it everywhere! Fully ISO 18013-5 compliant
- Change how identity is reported
- Cannot be counterfeited
Be Wallet Free
With GET Mobile ID
Make the Move to Secure Digital ID
Contact our Team to learn more!


